2.7 billion workers lack company email, managed devices, or app access and must be physically present for their jobs, according to BCG research. The compliance incident management programs meant to protect them assume those tools as a starting point.
Hazards on shop floors, loading docks, job sites, and patient care units go unreported because no pathway was ever built for the workers who see them first. A scalable framework has to solve that problem. The sections below map a seven-stage incident lifecycle to SOC 2, GDPR, and HIPAA obligations, starting with the intake and communication infrastructure that determines whether frontline incidents are recorded at all.
TL;DR
- A scalable framework maps seven incident stages to SOC 2, GDPR, and HIPAA requirements simultaneously
- Auto-classifying intake routes incidents to the correct regulatory notification workflow before deadlines expire
- Role-based access control must be scoped to site, purpose, and time to work across multiple regulatory zones
- AI-driven automation compresses response timelines and turns MTTD and MTTR data into regulatory evidence
- Frontline workers are the biggest compliance blind spot when intake requires apps, email, or computer access
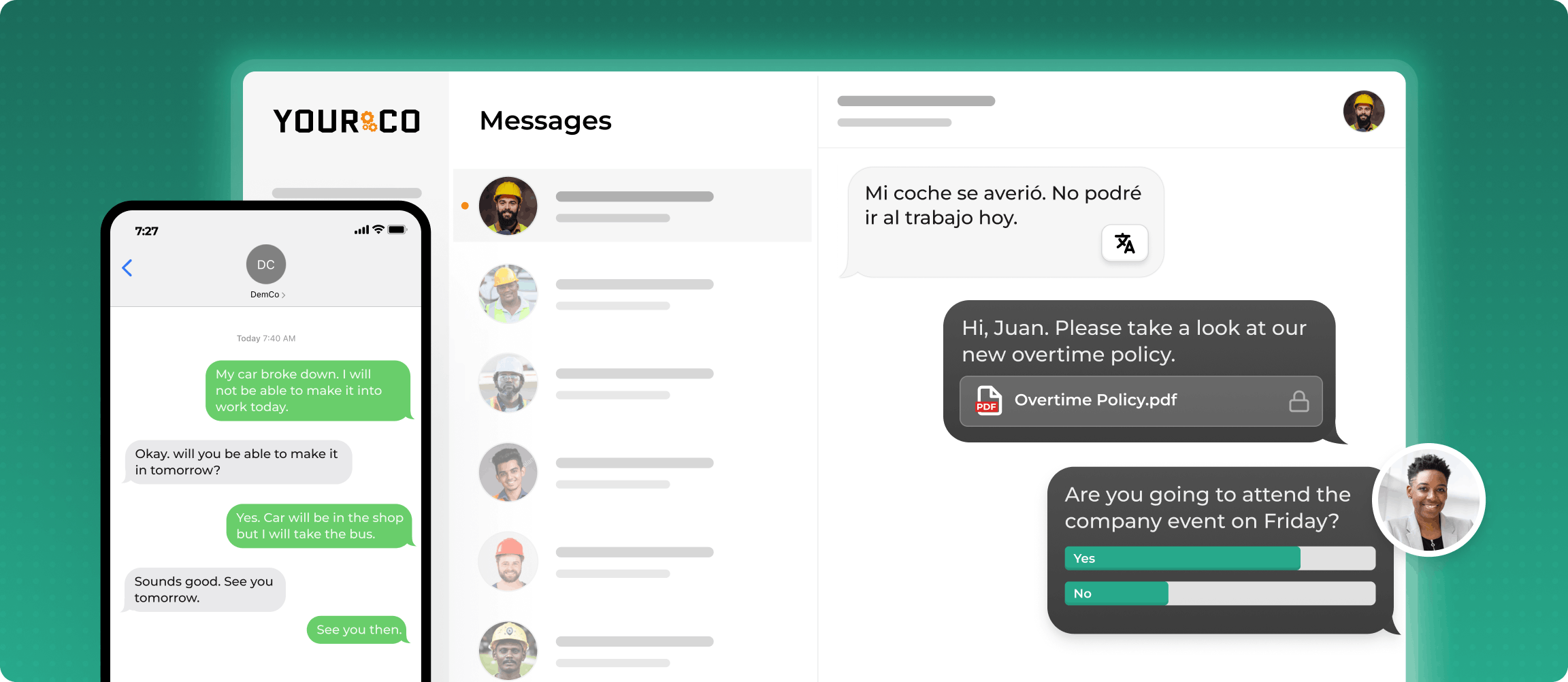
- SMS-based platforms like Yourco reach every worker on any phone, in any language, with timestamped, audit-ready records
Recognize Why Frontline Enterprises Face Unique Compliance Risks
Compliance incident management at enterprise scale depends on whether policies actually reach the people closest to the risk and pull information back from them. Workers without company email, managed devices, or app access are not negligent reporters; no reporting pathway was ever built for them. When compliance programs operate from recorded-only data, they manage a fraction of actual risk exposure.
93% of HR leaders believe clear safety communication reduces workplace incidents, according to a Yourco-commissioned survey of 150 HR leaders. That communication only reduces incidents when it actually reaches the workers performing the work, and the financial stakes compound by industry.
Frameworks only work when they reach the frontline, where incidents happen.
Align the 7-Stage Incident Lifecycle to Your Regulatory Obligations
This scalable framework integrates NIST SP 800-61r3 with the phases of ISO/IEC 27035-2:2023 and the notification requirements of Service Organization Control 2 (SOC 2), the General Data Protection Regulation (GDPR), and the Health Insurance Portability and Accountability Act (HIPAA) into a unified seven-stage process. Each stage carries its own deliverables, evidence, and timing expectations:
- Stage 1, Preparation: Establish an incident response policy and a communication plan with stakeholder templates; build playbooks by incident type (including AI agent incidents such as data exfiltration); run tabletop exercises; and name your response team.
- Stage 2, Detection & Analysis: Standardize how incidents enter the system. The GDPR clock starts at awareness, not at confirmation.
- Stage 3, Triage & Classification: Confirm whether an event is a verified incident, assign severity, and route to the correct notification workflow.
- Stage 4, Containment & Eradication: Preserve evidence before containment (isolation/firewalling), then eradicate (malware removal/config changes). Each action is timestamped and attributed to a named individual.
- Stage 5, Investigation: Identify root cause, gather forensic evidence, and prepare notification content.
- Stage 6, Resolution & Recovery: Return systems to operational readiness and execute regulatory notifications: GDPR within 72 hours, HIPAA within 60 days of discovery.
- Stage 7, Retrospective: Conduct a formal post-incident review. Produce root cause analysis, updated risk assessments, and revised playbooks.
This information is for general awareness only. For specific compliance guidance, consult with qualified legal professionals.
Standardize Intake to Eliminate Reporting Problems
The detection stage is where most frontline enterprises fail because when incident intake requires a corporate email login, a managed laptop, or an app installation, the workers most likely to encounter hazards firsthand are excluded from the process. 91% of HR leaders say SMS increases frontline employee response rates, according to a Yourco-commissioned survey of 150 HR leaders, which makes text the only channel that consistently reaches every worker at the moment an incident is discovered.
A standardized intake form, aligned with IRS standards and GDPR notification requirements, should capture the following minimum fields at the point of discovery.
Once those fields are captured, auto-classification routes incidents by severity. Critical incidents trigger parallel notification workflows immediately, while medium-severity events involving regulated data run the clock until they are ruled out. This routing logic eliminates the manual triage bottleneck that causes enterprises to miss GDPR and HIPAA notification windows.
Configure Role-Based Access That Satisfies Three Frameworks at Once
Role-based access control (RBAC) for compliance incident management is an HR and compliance governance decision, with implications well beyond IT configuration. NIST SP 800-162 establishes that for multi-site enterprises, pure RBAC is not sufficient on its own. Layered access controls evaluate the user, the record, and the regulatory environment simultaneously.
A single Compliance Officer role should carry different effective permissions depending on which site's data is being accessed. The core roles to define include:
- Global Compliance Officer: Read/write across all sites with step-up multi-factor authentication for protected health information access; cannot modify audit logs
- Regional/Site Compliance Officer: Read/write scoped to assigned sites only; escalation capability to global level
- HR Director: Access limited to HR-designated fields; all access purpose-tagged under GDPR Article 5(1)(b)
- IT Lead: Full access to technical security incidents; personal data content masked unless directly required for remediation
- Frontline Supervisor: Read/write for incidents they submitted or involving direct reports; automatically removed from records where they are named as a respondent
This structure aligns with HIPAA technical safeguards, GDPR Articles 25 and 32, and SOC 2 CC6 criteria.
Automate Detection and Resolution to Compress Your Response Timeline
Security teams that deploy AI and automation extensively are detecting and containing breaches faster than those that do not. The global average breach lifecycle fell to 241 days, a nine-year low, according to IBM's 2025 Cost of a Data Breach Report. Organizations that use AI and automation extensively shortened that figure by a further 80 days compared to those without these capabilities.
In manufacturing specifically, a 19% reduction in mean time to repair equipment (MTTR) and a 43% drop in emergency interventions came from AI-powered condition monitoring, according to a peer-reviewed study. Faster containment shortens regulatory notification windows and produces cleaner audit records.
Address Data Sovereignty and Shadow AI Before They Become Incidents
Two trends require attention from compliance teams managing distributed frontline operations. Both carry direct implications for how incident records are structured and retained.
Data sovereignty is now an active compliance category. One in three organizations experienced a data sovereignty-related incident in the preceding 12 months, including unauthorized cross-border transfers and regulatory investigations, according to a Kiteworks report. Many organizations now treat the data residency zone as a required attribute for every incident record, and Gartner research has identified Geopatriation as a top strategic technology trend for 2026.
Shadow AI extends the shadow IT problem into new regulatory territory. ISACA's 2025 analysis documents that unsanctioned AI tools undermine organizations' alignment with the NIST AI Risk Management Framework and the EU AI Act. When distributed workforces use unsanctioned AI tools, the resulting compliance exposure stays invisible to traditional audit processes.
Close the Frontline Communication Gap With Yourco
For enterprises, the hardest part of compliance incident management is moving information from the worker who experienced an incident to the system that needs to record it. Yourco closes that gap by reaching every worker through the channel that is already in their pocket.
- SMS to any phone: no app download, no Wi-Fi, no company email required. Works on smartphones and basic flip phones alike.
- Two-way messaging: workers report incidents, respond to safety alerts, and confirm policy acknowledgments through SMS.
- AI-powered translation: across 135+ languages and dialects, so multilingual teams can report and receive communications accurately.
Yourco integrates with 240+ HRIS and payroll systems, keeping employee directories current so that terminated workers lose access and new hires are automatically enrolled.
Enterprise Bridge enables corporate leadership to send centralized, one-way compliance updates across all locations, while local managers maintain direct communication with their teams.
Frontline Intelligence gives compliance and HR teams centralized visibility into safety communication patterns across all locations. It scans everyday messages for high-risk language, including safety concerns and indicators of interpersonal conflict, and surfaces real-time, site-level insights. Leadership can flag locations with slow response times to safety alerts and surface policy-acknowledgment gaps before they show up as audit findings.
"The Yourco texting system has helped the Railroad communicate with a 24/7 workforce. Sharing weather events, safety concerns and company bulletins have been priceless."
— Carl Kocur, Vice President, Engineering, New Orleans Public Belt Railroad
After 90 days on Yourco, companies see two-way employee engagement reach 86%.
Try Yourco for free today, or schedule a demo to see the difference the right workplace communication solution can make for your company.
Frequently Asked Questions About Compliance Incident Management
How do you build a compliance incident management framework for multiple regulations?
Align each stage of the seven-stage incident lifecycle with the specific documentation and notification requirements of each applicable regulation. A centralized system with auto-classification routes incidents to the correct regulatory workflow at triage, ensuring parallel notification timelines are managed from a single record.
What is the biggest compliance risk for enterprises with frontline workers?
Incident underreporting is the most significant risk. When reporting pathways require corporate email, managed devices, or app installations, frontline workers are structurally excluded from the intake process. SMS-based platforms like Yourco provide accessible reporting channels that work on any phone, with no downloads or training required.
How does role-based access control work for multi-site compliance systems?
Effective role-based access control for compliance incident management evaluates three factors simultaneously: the user's role, the specific record being accessed, and the regulatory environment governing that record's jurisdiction. A single role, such as Compliance Officer, should have different effective permissions depending on whether the data falls under GDPR, HIPAA, or SOC 2 requirements.
What is a realistic MTTR improvement from automation?
Organizations using AI and automation extensively in their incident response see meaningful reductions in mean time to resolve. Shorter breach lifecycles cut both financial exposure and regulatory risk.
Why do compliance frameworks need to account for data sovereignty?
A significant share of organizations have experienced data sovereignty-related incidents in recent years, including unauthorized cross-border transfers and regulatory investigations. Incident records capture where data resided at the time of the event, which regulatory regime governs, and which notification timeline applies, because a single incident can trigger multiple regional obligations simultaneously.